Use VCE Exam Simulator to open VCE files

Microsoft MB-300 Practice Test Questions, Microsoft MB-300 Exam Dumps
With Examsnap's complete exam preparation package covering the Microsoft MB-300 Practice Test Questions and answers, study guide, and video training course are included in the premium bundle. Microsoft MB-300 Exam Dumps and Practice Test Questions come in the VCE format to provide you with an exam testing environment and boosts your confidence Read More.
The Microsoft Dynamics 365: Core Finance and Operations MB-300 exam is a critical certification for professionals who want to demonstrate their skills and knowledge in implementing and managing business processes within the Dynamics 365 environment. This exam tests the understanding of core finance and operations functionalities, configuration, and integration capabilities of Dynamics 365. For aspiring candidates, understanding the exam objectives, structure, and the technologies involved is the first step toward passing the MB-300 exam successfully. This article explores the components of the MB-300 exam, provides insights into Dynamics 365 Core Finance and Operations, and offers guidance for preparing an effective study plan.
Microsoft Dynamics 365 is an enterprise resource planning (ERP) and customer relationship management (CRM) platform designed to help organizations manage their business operations efficiently. The platform integrates finance, operations, sales, marketing, and customer service, allowing businesses to streamline workflows, gain actionable insights, and make informed decisions. Dynamics 365 is modular, which means companies can deploy specific modules such as finance, supply chain management, or human resources according to their needs, providing flexibility and scalability.
The Core Finance and Operations module focuses on financial management, operational efficiency, and seamless integration between departments. Understanding this module is essential for anyone preparing for the MB-300 exam because it forms the foundation of Dynamics 365 functionality. It covers finance processes such as accounts payable, accounts receivable, budgeting, and general ledger management, as well as operational processes like procurement, inventory management, and order fulfillment. Candidates who grasp these concepts are better equipped to configure and optimize Dynamics 365 for real-world business scenarios.
Obtaining the MB-300 certification is not just about passing an exam; it validates a professional’s ability to implement and manage Dynamics 365 solutions effectively. Organizations increasingly rely on Dynamics 365 to integrate their financial and operational systems, and certified professionals are highly sought after. The certification demonstrates competency in core business processes, the ability to configure applications, and the skill to integrate Dynamics 365 with other Microsoft services.
MB-300 certification also enhances career prospects by opening doors to roles such as Dynamics 365 functional consultant, business analyst, ERP consultant, or solution architect. For those already working in finance or operations, this certification provides recognition of expertise, which can lead to promotions, higher salaries, and leadership opportunities. Beyond personal benefits, certified professionals help organizations optimize their systems, reduce errors, and ensure compliance with financial regulations.
The MB-300 exam assesses a candidate’s understanding of the fundamental aspects of Dynamics 365 finance and operations. The exam covers multiple domains, each of which focuses on a specific area of functionality. Candidates should familiarize themselves with the exam objectives before starting their preparation because understanding the scope and weight of each domain helps in prioritizing study efforts. The key domains include core finance and operations concepts, implementation of business processes, configuration of applications, and integration and data management.
Core finance and operations concepts focus on understanding the basic modules, navigation, and system features. Candidates should know how to configure general ledger, manage financial transactions, and implement standard accounting practices. Implementation of business processes involves mapping business requirements to Dynamics 365 functionality. This includes designing workflows, automating processes, and ensuring alignment with organizational objectives. Configuration of applications covers setting up modules such as accounts payable, accounts receivable, inventory, and procurement. Integration and data management focus on connecting Dynamics 365 to other Microsoft services, migrating data, and ensuring data integrity and security.
The MB-300 exam typically includes multiple-choice questions, scenario-based questions, and case studies that simulate real-world situations. Understanding the format helps candidates practice time management and approach questions strategically. Microsoft periodically updates the exam to reflect the latest version of Dynamics 365, so staying current with new features and functionalities is essential for success.
Core finance and operations functionality is at the heart of Dynamics 365. Finance modules cover areas such as general ledger, accounts payable, accounts receivable, budgeting, and fixed assets. Candidates must understand how these modules interact and how financial data flows through the system. For example, posting a transaction in accounts payable should automatically update the general ledger and impact financial reports. Knowledge of financial dimensions, ledger setup, and reporting is crucial for ensuring accurate and efficient financial management.
Operations modules focus on procurement, inventory, warehouse management, and order fulfillment. Candidates should know how to manage the supply chain, configure product information, track inventory, and handle procurement processes. Understanding operational workflows helps in designing solutions that reduce bottlenecks and improve efficiency. Additionally, Dynamics 365 allows organizations to configure security roles, user permissions, and workflow automation, making it important for candidates to understand how to implement these configurations correctly.
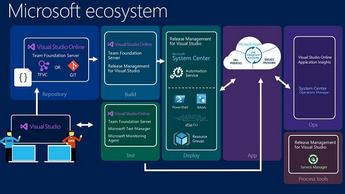
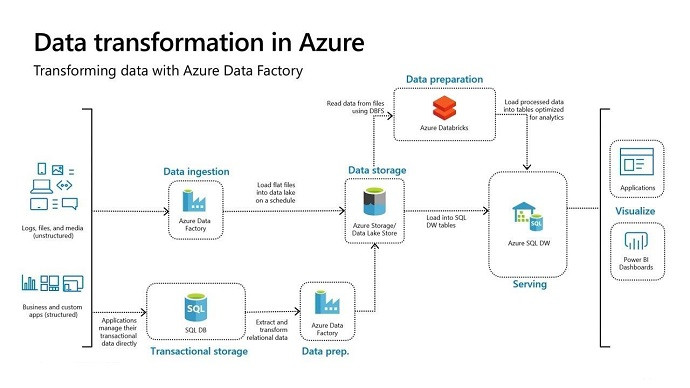
Integration capabilities are another key aspect of Dynamics 365. The platform connects with Microsoft Power Platform, Office 365, and Azure services, allowing organizations to automate processes, generate reports, and analyze data seamlessly. For example, integrating Power BI with Dynamics 365 provides real-time financial insights, while using Power Automate helps automate repetitive operational tasks. Candidates preparing for the MB-300 exam should be familiar with these integration points and know how to configure them in practical scenarios.
The first step in preparing for the MB-300 exam is analyzing the official exam objectives. Microsoft provides a detailed exam guide that outlines the topics covered, their weightage, and recommended study resources. By reviewing the exam objectives, candidates can identify areas of strength and weakness, plan their study schedule, and focus on high-priority topics.
For instance, if a candidate is already familiar with financial modules but less experienced with supply chain management, they can allocate more time to operations processes. Understanding the objectives also helps in identifying the type of questions likely to appear in the exam, whether scenario-based or conceptual. Additionally, candidates can use the exam guide to select relevant learning resources, such as official documentation, online courses, and hands-on labs, which align with each domain.
A structured study plan is essential for success in the MB-300 exam. Candidates should allocate sufficient time to cover each domain, practice hands-on exercises, and review key concepts regularly. A study plan should include daily or weekly goals, milestones, and self-assessment checkpoints to monitor progress. Breaking down the content into manageable sections prevents overwhelm and ensures consistent preparation.
When creating a study plan, it is important to balance theoretical learning with practical experience. Reading the official study guide provides foundational knowledge, while working in a Dynamics 365 environment reinforces learning through real-world application. Practice exams should be incorporated into the study plan to assess readiness, identify knowledge gaps, and improve exam-taking strategies. A disciplined and structured approach significantly increases the chances of passing the MB-300 exam on the first attempt.
Hands-on experience is crucial for mastering Dynamics 365 Core Finance and Operations. Practical exercises allow candidates to explore system navigation, configure modules, and simulate business processes. By working in a sandbox environment, candidates can test scenarios such as posting invoices, managing inventory, or creating financial reports without affecting real data. This experiential learning reinforces theoretical knowledge and builds confidence for the actual exam.
Hands-on practice also helps candidates understand how different modules interact. For example, configuring an order fulfillment process in operations affects inventory levels, financial postings, and reporting. Understanding these relationships is essential for designing efficient workflows and ensuring accurate data processing. Candidates who dedicate sufficient time to practical exercises often find it easier to answer scenario-based questions in the MB-300 exam.
Microsoft provides a wealth of learning resources for MB-300 candidates. The official study guide outlines exam objectives and recommended documentation, while Microsoft Learn offers interactive tutorials and modules. Online courses on platforms such as Udemy, LinkedIn Learning, and Coursera provide structured content, quizzes, and real-world scenarios to reinforce learning. Candidates can also use video tutorials, blogs, and discussion forums to clarify concepts and gain insights from experienced professionals.
Study groups and online communities are valuable resources for exam preparation. Engaging with other aspirants allows candidates to discuss complex topics, share tips, and access additional learning materials. Many communities also provide insights into common exam challenges, helping candidates avoid pitfalls and focus on critical concepts. Combining multiple learning resources ensures comprehensive preparation and increases confidence for the MB-300 exam.
Microsoft Dynamics 365 evolves continuously, and the MB-300 exam is updated periodically to reflect new features and functionalities. Candidates should stay informed about updates to the platform, such as changes in finance or operations modules, integration capabilities, or reporting features. Monitoring Microsoft’s official announcements, blogs, and release notes helps candidates remain current and ensures their knowledge aligns with the latest exam objectives.
Staying updated also prevents surprises during the exam. For example, a new workflow feature in Dynamics 365 may be tested in the MB-300 exam. Candidates who are aware of such updates can review documentation, practice using the feature, and incorporate it into their study plan. Regularly checking official resources and participating in community discussions helps maintain up-to-date knowledge and improves exam readiness.
Understanding the MB-300 exam structure and managing time effectively is crucial for success. The exam typically consists of multiple-choice and scenario-based questions that require careful reading and analysis. Candidates should practice pacing themselves to answer all questions within the allocated time. Developing an exam strategy, such as tackling easier questions first and marking difficult ones for review, helps optimize performance.
Scenario-based questions often require applying knowledge to real-world business situations. Candidates should approach these questions by identifying the problem, considering relevant modules, and choosing the most effective solution. Practicing with sample exams and simulations helps candidates develop critical thinking skills, reinforces knowledge, and improves decision-making under time constraints.
Preparing for the Microsoft Dynamics 365: Core Finance and Operations MB-300 exam requires a structured approach that balances theoretical knowledge with practical experience. The exam tests both conceptual understanding and the ability to apply Dynamics 365 functionalities in real-world business scenarios. To succeed, candidates must leverage multiple learning resources, develop effective study habits, and engage with practical exercises to reinforce their knowledge. We explore study techniques, recommended resources, and strategies that can help candidates prepare efficiently for the MB-300 exam.
The first step in MB-300 exam preparation is reviewing the official Microsoft study guide. Microsoft provides a detailed outline of exam objectives, which serves as the foundation for a focused study plan. The study guide highlights critical areas such as core finance and operations concepts, implementation of business processes, configuration of applications, and integration and data management. By following the guide, candidates ensure they cover all required topics and avoid spending excessive time on irrelevant content.
Exam objectives in the study guide include understanding financial management processes such as accounts payable, accounts receivable, general ledger configuration, and budgeting. Operations topics cover procurement, inventory management, and supply chain workflows. Integration and data management topics focus on connecting Dynamics 365 to other Microsoft services and ensuring accurate data migration. Reviewing these objectives helps candidates identify personal knowledge gaps, enabling them to allocate study time effectively to areas that need the most attention.
The study guide also provides links to official documentation, training modules, and sample exercises. Using these resources in conjunction with the guide ensures comprehensive preparation. Candidates should read the guide carefully, take notes, and create summaries of key concepts to reinforce understanding. A thorough review of the official study guide is essential to establish a solid foundation for deeper learning.
Online courses and tutorials are highly effective tools for MB-300 exam preparation. Many platforms, including Microsoft Learn, Udemy, LinkedIn Learning, and Coursera, offer structured content that aligns with exam objectives. These courses often include interactive exercises, quizzes, and scenario-based learning that reinforce conceptual understanding. By following an online course, candidates can progress systematically through core topics and gain exposure to real-world examples.
Interactive learning platforms allow candidates to apply their knowledge immediately. For example, exercises on configuring accounts payable or managing inventory in a sandbox environment help solidify theoretical concepts. Video tutorials provide step-by-step guidance, demonstrating how to navigate Dynamics 365 modules and perform essential tasks. Engaging with online courses ensures that learning is not limited to reading materials but includes active participation and practice.
Candidates should choose courses that cover both finance and operations modules comprehensively. Some courses focus more on finance, while others emphasize supply chain and operational workflows. Selecting a course that balances both areas helps ensure well-rounded preparation. In addition, many online courses include practice exams and assessments, which allow candidates to gauge their readiness and identify areas for improvement before attempting the official MB-300 exam.
Hands-on experience is a critical component of MB-300 exam preparation. Theory alone is insufficient for understanding Dynamics 365, as the exam often includes scenario-based questions that require practical application of concepts. Setting up a test environment or sandbox instance of Dynamics 365 allows candidates to explore system functionalities, configure modules, and simulate business processes safely. Practicing with hands-on labs reinforces learning and builds confidence in applying knowledge.
Working in a sandbox environment provides opportunities to experiment with various configurations. For instance, candidates can simulate posting invoices, managing inventory transactions, setting up workflows, and integrating data from external sources. This experiential learning helps candidates understand how different modules interact and how changes in one module affect other processes. Hands-on labs also allow candidates to test error handling and troubleshoot issues, which is essential for real-world scenarios.
Practical exercises help develop critical thinking and problem-solving skills. Candidates learn to analyze business requirements, map them to Dynamics 365 functionalities, and implement efficient solutions. Regular hands-on practice also improves speed and accuracy, reducing the likelihood of errors during the exam. Candidates who dedicate sufficient time to hands-on labs often perform better on scenario-based questions, as they can draw from practical experience to choose the correct approach.
Practice exams are an essential tool for MB-300 preparation. They simulate the structure and difficulty of the real exam, helping candidates become familiar with question formats, timing, and exam expectations. By taking practice exams, candidates can assess their knowledge, identify weak areas, and refine study strategies. Frequent practice also reduces exam anxiety and improves confidence on test day.
When using practice exams, it is important to review both correct and incorrect answers. Analyzing mistakes provides insights into knowledge gaps and misconceptions. Candidates should focus on understanding why a particular answer is correct and how it applies to real-world scenarios. This approach reinforces learning and ensures that candidates can apply concepts in the exam rather than relying solely on memorization.
Practice exams also help with time management. The MB-300 exam includes multiple-choice and scenario-based questions, which can be time-consuming if not approached strategically. By simulating exam conditions during practice sessions, candidates can develop pacing strategies, ensuring they have enough time to answer all questions accurately. Regular practice, combined with careful review of results, strengthens readiness for the official MB-300 exam.
Study groups and online communities provide valuable support for MB-300 exam preparation. Connecting with other candidates allows for the exchange of ideas, discussion of challenging topics, and sharing of learning resources. Many study groups also provide insights into common pitfalls, exam patterns, and effective strategies for mastering Dynamics 365 Core Finance and Operations.
Engaging with a study group encourages accountability and consistent study habits. Candidates can participate in group exercises, simulate exam questions, and review each other’s understanding of key concepts. Online forums and discussion boards are additional resources where candidates can ask questions, clarify doubts, and learn from experienced professionals who have already passed the MB-300 exam.
Communities often share real-world scenarios that supplement official study materials. These examples help candidates understand how Dynamics 365 is applied in business settings, providing context for exam questions. By actively participating in study groups and forums, candidates expand their knowledge, gain new perspectives, and feel more confident about tackling the MB-300 exam.
Organizing study materials effectively is a crucial aspect of exam preparation. Candidates should gather resources such as official documentation, online courses, video tutorials, practice exams, and notes from study groups. Categorizing materials by topic or exam domain allows for focused study sessions and easier review. Well-organized materials reduce confusion, save time, and enhance retention.
Creating summaries, charts, and flow diagrams helps visualize complex processes in Dynamics 365. For example, mapping the flow of financial transactions or supply chain processes aids understanding and makes it easier to recall information during the exam. Candidates can also maintain a list of frequently asked questions, common errors, and important configurations, which serves as a quick reference for revision.
Time management is closely tied to organizing study materials. Candidates should allocate study sessions for reading, hands-on practice, and taking practice exams. Rotating between different types of learning activities keeps study sessions engaging and helps reinforce knowledge from multiple angles. A structured approach to study materials ensures comprehensive coverage of all exam objectives.
A well-planned study schedule is essential for MB-300 preparation. Candidates should set realistic goals, break down topics into manageable sections, and establish milestones for self-assessment. A study schedule should balance reading, hands-on practice, and review sessions to cover all exam objectives effectively.
When creating a schedule, it is important to allocate time according to personal strengths and weaknesses. Topics that are more challenging should receive more focus, while areas of strength can be reviewed periodically to reinforce retention. Including short breaks and flexible study sessions helps maintain focus and prevents burnout during long preparation periods.
Consistency is key to success in MB-300 preparation. Candidates should commit to a daily or weekly routine, dedicating sufficient time to study and practice. Regular assessments and self-evaluation ensure steady progress and identify areas that require additional attention. Following a structured study schedule enhances learning efficiency and increases the likelihood of passing the exam.
Successful MB-300 preparation requires a balance between theoretical knowledge and practical application. Reading official documentation and studying concepts provides the foundation, while hands-on practice and scenario simulations reinforce learning. Combining both approaches ensures that candidates can apply concepts effectively in the exam and in real-world business situations.
Practical exercises should be integrated with theoretical study. For example, after learning about configuring general ledger accounts, candidates should practice setting up accounts in a sandbox environment. Similarly, after studying procurement processes, they can simulate purchase orders and inventory management workflows. This combined approach strengthens understanding and improves recall during the exam.
Scenario-based practice is particularly valuable for MB-300 candidates. The exam often presents business situations where candidates must determine the best approach to achieve objectives using Dynamics 365 functionalities. By simulating these scenarios during preparation, candidates develop problem-solving skills, analytical thinking, and the ability to apply knowledge under time constraints.
Passing the Microsoft Dynamics 365: Core Finance and Operations MB-300 exam requires not only understanding theoretical concepts but also mastering their practical application. The exam assesses the ability to implement business processes, configure applications, and manage integrations within the Dynamics 365 environment. To achieve success, candidates must dedicate significant effort to practicing real-world scenarios, reinforcing their knowledge of core finance and operations modules, and developing strategies to tackle complex exam questions. This article explores methods for practicing, mastering core concepts, and ensuring readiness for the MB-300 exam.
Practice exams are one of the most effective tools for preparing for MB-300. They provide a simulation of the actual exam environment, enabling candidates to become familiar with question formats, timing constraints, and scenario-based problem-solving. Practice exams help identify knowledge gaps, reveal areas that require further study, and build confidence in answering complex questions. Regularly taking practice exams also reduces anxiety, as candidates gain experience working under exam conditions.
When using practice exams, it is crucial to review both correct and incorrect answers. Understanding why an answer is correct, and why alternatives are not, deepens comprehension of the material. Scenario-based questions often require applying multiple concepts simultaneously, so analyzing each response helps candidates develop logical reasoning skills. By combining practice exams with review sessions, candidates reinforce their knowledge and are better equipped to handle the challenges of the MB-300 exam.
Mastering core finance and operations concepts is essential for MB-300 success. Finance topics include general ledger configuration, accounts payable and receivable, budgeting, and fixed asset management. Candidates should understand how these modules interconnect, how transactions flow through the system, and how financial data impacts reporting. For example, posting a payment in accounts payable should automatically update the general ledger and reflect in financial statements. Understanding these relationships ensures accuracy and efficiency in business processes.
Operations topics cover procurement, inventory management, warehouse management, and order fulfillment. Candidates should focus on configuring modules, managing supply chain processes, and understanding how operational activities affect finance and reporting. Knowledge of product information management, warehouse setup, and procurement workflows is crucial for implementing effective business solutions. Integrating operational and financial processes provides a holistic understanding of Dynamics 365 Core Finance and Operations, which is often tested in scenario-based exam questions.
Simulating real-world business scenarios is a critical component of MB-300 preparation. The exam frequently presents complex situations that require candidates to determine the most effective solution using Dynamics 365 functionality. Practicing these scenarios helps candidates understand how different modules interact and how changes in one area affect overall business processes. For instance, creating a purchase order impacts inventory levels, vendor accounts, and financial postings. By practicing these scenarios, candidates develop practical skills and improve their ability to answer scenario-based questions accurately.
Scenario simulations can be conducted using a sandbox or test environment in Dynamics 365. Candidates should practice configuring modules, processing transactions, generating reports, and troubleshooting errors. Simulating end-to-end workflows, such as order-to-cash or procure-to-pay processes, reinforces understanding of how various modules work together. This experiential learning enhances retention, builds confidence, and prepares candidates for real-world application of Dynamics 365 concepts.
Understanding the integration between finance, supply chain, and operations is vital for MB-300 success. Dynamics 365 is designed to provide seamless connectivity between modules, ensuring accurate data flow and efficient business processes. Candidates should learn how financial transactions impact operational activities and vice versa. For example, a sales order affects inventory, revenue recognition, and accounts receivable. Mastering these integrations ensures candidates can address questions that involve multiple functional areas.
Integration also includes connecting Dynamics 365 to other Microsoft services such as Power BI, Power Automate, and Office 365. Candidates should understand how to leverage these integrations to automate workflows, generate reports, and analyze data. For instance, integrating Power BI with Dynamics 365 provides real-time insights into financial and operational performance, while Power Automate can streamline repetitive tasks. Knowledge of these integrations demonstrates a candidate’s ability to implement efficient solutions and is often tested in the MB-300 exam.
Many candidates encounter challenges when preparing for MB-300, particularly with scenario-based questions and module integrations. Common difficulties include understanding complex workflows, managing multiple modules simultaneously, and applying theoretical concepts to practical situations. To overcome these challenges, candidates should practice problem-solving, review case studies, and analyze real-world examples. Breaking down complex scenarios into smaller components helps clarify the steps needed to implement solutions effectively.
Another common challenge is managing time during the exam. Scenario-based questions can be lengthy and require careful analysis. Candidates should practice pacing themselves, prioritizing easier questions first, and revisiting difficult scenarios after completing the rest of the exam. Time management skills, combined with scenario practice, improve accuracy and reduce the likelihood of incomplete answers.
Data management and migration are critical topics in Dynamics 365 Core Finance and Operations. Candidates should understand how to import, export, and maintain data accurately across modules. For example, migrating vendor or customer information must be done carefully to avoid errors in financial or operational processes. Knowledge of data templates, data entities, and validation rules is essential for ensuring successful data migration.
Candidates should also practice handling data exceptions and performing reconciliations. Understanding how to identify and correct discrepancies between financial records and operational transactions is crucial for maintaining data integrity. Practice exercises involving data migration scenarios help candidates develop the skills needed to manage large datasets and ensure accurate reporting, which is frequently assessed in the MB-300 exam.
Workflow configuration is a key area of MB-300. Candidates should be familiar with setting up approval processes, automating routine tasks, and defining business rules within Dynamics 365. Workflows improve efficiency, reduce errors, and ensure compliance with organizational policies. Understanding how to design workflows for finance and operations modules is essential for implementing effective business processes.
Automation can be applied in areas such as purchase order approvals, invoice processing, and inventory management. Candidates should practice configuring automated notifications, task assignments, and exception handling. By mastering workflow configuration and automation, candidates demonstrate the ability to optimize processes, which is a critical aspect of both exam scenarios and real-world implementation.
Security and user role management are important for MB-300 candidates to understand. Dynamics 365 allows administrators to assign roles, define permissions, and control access to sensitive financial and operational data. Candidates should practice setting up security roles, configuring access levels, and managing user privileges to ensure that employees can perform their tasks without compromising data integrity.
Understanding security configuration is crucial for scenarios involving multiple users or departments. For example, accounts payable clerks should have access to vendor invoices but not to general ledger configurations. Candidates should practice implementing role-based security and testing permissions to verify that access is appropriately restricted. Mastery of security concepts ensures candidates can design secure and efficient solutions in Dynamics 365.
Reporting and analytics are integral to finance and operations processes in Dynamics 365. Candidates should understand how to generate financial statements, operational reports, and performance dashboards. Knowledge of reporting tools such as Power BI and built-in Dynamics 365 reporting features is essential for analyzing data and making informed decisions.
Candidates should practice creating custom reports, applying filters, and interpreting data trends. Scenario-based questions often require analyzing reports to identify issues, recommend solutions, or optimize processes. Proficiency in reporting and analytics ensures candidates can provide actionable insights, which is a key component of the MB-300 exam and real-world business operations.
Mastery of Dynamics 365 Core Finance and Operations requires continuous learning. Candidates should review key concepts regularly, practice new features, and stay informed about updates to the platform. Dynamics 365 evolves frequently, introducing new functionalities that may appear in the MB-300 exam. Keeping up-to-date ensures that candidates remain competent and confident in their knowledge.
Knowledge reinforcement can be achieved through daily practice, reviewing study notes, and engaging with learning communities. Participating in forums, attending webinars, and reading blogs about Dynamics 365 provide additional insights and practical examples. Continuous learning helps candidates internalize concepts, identify knowledge gaps, and improve their ability to handle complex scenarios during the exam.
Successful MB-300 preparation requires a balance between theoretical understanding and practical application. Candidates should study core concepts from official documentation, online courses, and study guides while applying that knowledge in hands-on exercises and scenario simulations. Combining both approaches ensures comprehensive mastery and the ability to address real-world challenges effectively.
For example, after studying accounts receivable workflows, candidates should practice creating customer invoices, posting payments, and generating reports in a sandbox environment. Similarly, learning about procurement processes should be complemented with exercises in purchase order creation, approval workflows, and vendor management. This integrated approach strengthens comprehension, reinforces retention, and prepares candidates to excel in the MB-300 exam.
Repetition is a key strategy for reinforcing learning and building confidence. Candidates should repeatedly practice configurations, transactions, and scenarios until the processes become second nature. Repetition helps solidify understanding, reduces errors, and ensures that candidates can answer scenario-based questions accurately under exam conditions.
Regular review sessions, combined with hands-on exercises and practice exams, enhance memory retention and improve problem-solving skills. Candidates who consistently practice and reinforce their knowledge feel more confident, which directly impacts performance on the MB-300 exam. Building confidence through repetition ensures that candidates are well-prepared to handle both theoretical and practical challenges.
The Microsoft Dynamics 365: Core Finance and Operations MB-300 exam represents the culmination of months of preparation, hands-on practice, and mastering of core finance and operations concepts. Successfully navigating the exam requires more than understanding the material; it demands strategic planning, time management, and an understanding of how to approach questions effectively. Beyond the exam itself, certification opens doors to career advancement and opportunities for applying knowledge in real-world business contexts. We explored strategies for exam day, preparation techniques for maximizing performance, and guidance on leveraging certification for professional growth.
Mental and physical preparation is a crucial, often overlooked, component of success on the MB-300 exam. A well-rested mind and a focused, alert body improve concentration, decision-making, and the ability to handle complex scenario-based questions. Candidates should ensure adequate sleep in the days leading up to the exam, maintain healthy nutrition, and engage in light exercise to reduce stress and increase energy levels. Mental preparation involves cultivating confidence, visualizing success, and employing relaxation techniques such as deep breathing to remain calm during the exam.
A positive mindset plays a significant role in performance. Candidates should remind themselves of the preparation and practice they have completed and approach the exam with a problem-solving attitude. Avoiding last-minute cramming reduces anxiety and helps retain information more effectively. Mental and physical readiness sets the stage for optimal performance, ensuring candidates can apply their knowledge without distractions or stress.
Strategic review of key concepts is essential in the final stages of MB-300 preparation. Candidates should focus on areas where they feel less confident or where practice exams have revealed gaps in understanding. Reviewing critical finance and operations modules, such as general ledger, accounts payable, procurement, and inventory management, reinforces knowledge and ensures that candidates can respond accurately to scenario-based questions.
In addition to revisiting core modules, candidates should review workflow configurations, security roles, integration points, and reporting tools. These topics often appear in real-world exam scenarios and require an understanding of how different modules interact. Creating condensed notes, charts, or flow diagrams can help with quick revision, allowing candidates to visualize processes and retain critical information effectively. Strategic review ensures that knowledge is fresh and accessible during the exam.
Effective time management is crucial when taking the MB-300 exam. The exam typically includes multiple-choice and scenario-based questions that require careful reading and analysis. Candidates should allocate time according to the complexity of questions, ensuring that all items are addressed. A practical approach is to answer simpler questions first, marking more challenging scenarios for review later. This strategy prevents spending excessive time on individual questions and maximizes overall performance.
Scenario-based questions often require evaluating multiple options and understanding the implications of each choice. Candidates should read each scenario carefully, identify the core problem, and analyze how various modules or processes are affected. Efficient time management, combined with methodical analysis, ensures that candidates can tackle all questions effectively while minimizing errors caused by rushed responses.
Scenario-based questions are a hallmark of the MB-300 exam. These questions present complex business situations and require candidates to apply their knowledge to identify the most appropriate solution. Approaching these questions systematically is essential. Candidates should first understand the scenario, then consider the relevant modules, processes, and integration points before selecting the best course of action. Breaking down scenarios into smaller components helps clarify the problem and facilitates logical decision-making.
Candidates should also be mindful of the nuances in wording, as exam questions may test subtle differences in functionality or process implementation. Paying close attention to details such as workflow dependencies, financial postings, or operational constraints ensures that responses are accurate. Practicing scenario-based questions during preparation builds familiarity, confidence, and the ability to handle complex exam challenges.
Stress management during the MB-300 exam is vital for maintaining performance. Anxiety or pressure can impair judgment, reduce concentration, and increase the likelihood of errors. Candidates should employ techniques such as deep breathing, mindfulness, or brief mental breaks to stay calm and focused. Staying hydrated, maintaining a comfortable pace, and avoiding distraction are practical strategies for minimizing stress during the exam.
Maintaining focus involves reading each question carefully, analyzing all options, and resisting the urge to rush. Candidates should trust their preparation and approach each scenario methodically. By managing stress effectively, candidates can think clearly, apply knowledge accurately, and maximize their chances of success on the MB-300 exam.
Obtaining the MB-300 certification demonstrates expertise in Dynamics 365 Core Finance and Operations, making candidates valuable assets to organizations. Certification opens doors to roles such as Dynamics 365 functional consultant, ERP consultant, business analyst, or solution architect. Employers recognize the certification as evidence of practical knowledge, problem-solving ability, and the capacity to implement integrated business solutions.
Certified professionals can leverage their credentials for career advancement, including promotions, salary increases, or leadership opportunities. In addition, MB-300 certification enhances credibility when consulting with clients, managing projects, or leading implementation teams. Professionals can use the certification as a foundation for pursuing additional Dynamics 365 credentials or specialized certifications, further expanding their expertise and career prospects.
The MB-300 exam reflects a specific version of Dynamics 365, but the platform evolves continuously. Candidates who achieve certification should continue learning to maintain relevance and proficiency. Staying current with new features, updates, and best practices ensures that certified professionals can apply their knowledge effectively in business environments. Engaging with online communities, attending webinars, and exploring new modules keeps skills sharp and enhances career growth.
Continuous learning also prepares professionals for advanced certifications or specialized roles. For example, after earning MB-300, candidates might pursue certifications in Dynamics 365 finance, supply chain, or human resources modules. Ongoing learning demonstrates commitment to professional development, enhances problem-solving capabilities, and increases opportunities for leadership or consulting roles within organizations using Dynamics 365.
The knowledge gained through MB-300 preparation and certification is highly applicable in real-world business environments. Certified professionals can design and implement workflows, configure financial and operational modules, and integrate systems to optimize processes. Applying this knowledge enhances organizational efficiency, reduces errors, and ensures compliance with financial regulations and operational standards.
Professionals can also contribute to strategic decision-making by analyzing data, generating reports, and providing insights derived from Dynamics 365 systems. Understanding how to leverage the platform for process automation, reporting, and integration enables certified individuals to recommend solutions that improve productivity, reduce costs, and support organizational objectives. Applying certification knowledge effectively reinforces the value of the MB-300 credential.
Certification provides opportunities to expand professional networks. Engaging with peers, mentors, and experts in Dynamics 365 communities enhances learning, offers guidance on implementation challenges, and facilitates knowledge sharing. Networking allows certified professionals to exchange insights, access resources, and discover new career opportunities within organizations leveraging Dynamics 365 solutions.
Professional networking also supports continuous development by exposing certified individuals to industry trends, best practices, and emerging technologies. By participating in forums, attending conferences, and collaborating on projects, professionals enhance their expertise, build credibility, and increase visibility in the Dynamics 365 community. Networking complements technical skills, providing a platform for career growth and recognition.
MB-300 certification establishes a foundation in Core Finance and Operations, but Dynamics 365 includes additional specialized modules such as advanced finance, supply chain planning, human resources, and customer engagement. Certified professionals can explore these advanced modules to expand their expertise and pursue targeted roles. Understanding the interconnections between modules enhances problem-solving capabilities and enables the design of comprehensive business solutions.
Exploring advanced modules also prepares professionals for higher-level certifications and consulting opportunities. For example, mastering supply chain planning in conjunction with finance and operations knowledge allows professionals to optimize end-to-end business processes. Continuous exploration of Dynamics 365 capabilities ensures that certified individuals remain competitive and valuable to organizations seeking expertise in integrated business solutions.
Many professionals use MB-300 certification as a stepping stone to consulting or implementation roles. In these positions, knowledge of finance and operations modules, workflow configuration, and integration is applied to design solutions for clients. Preparing for such roles involves practicing project scenarios, developing implementation plans, and understanding client requirements. Certification validates the ability to execute these tasks effectively, making professionals competitive candidates for consulting engagements.
Implementation roles often require adapting Dynamics 365 functionalities to unique organizational needs. Certified professionals must be able to analyze business processes, recommend configurations, and troubleshoot challenges. Hands-on experience, scenario practice, and knowledge of integration tools prepare candidates to deliver successful implementations, demonstrating the practical value of MB-300 certification in professional settings.
Problem-solving is a critical skill for Dynamics 365 professionals. MB-300 preparation emphasizes understanding workflows, module interactions, and integration capabilities, which provide a foundation for addressing real-world business challenges. Certified individuals can analyze processes, identify inefficiencies, and design solutions that optimize operations and improve financial accuracy.
Developing problem-solving skills involves practicing scenario-based questions, experimenting with configurations in sandbox environments, and reviewing case studies. Candidates learn to evaluate multiple options, consider system implications, and select the most effective solution. Strong problem-solving abilities enhance performance in the MB-300 exam and prepare professionals to apply their knowledge effectively in business contexts.
Dynamics 365 evolves with regular updates, introducing new features, functionalities, and integration options. Maintaining the relevance of MB-300 certification requires staying informed about platform changes, exploring new tools, and adapting existing knowledge to current versions. Professionals should regularly review Microsoft release notes, participate in training programs, and engage with the community to remain proficient.
Maintaining certification relevance ensures that professionals can apply the latest best practices, leverage new capabilities, and provide up-to-date solutions for their organizations. Continuous engagement with the platform and ongoing learning reinforce expertise, enhance career opportunities, and maximize the return on investment in MB-300 certification.
MB-300 certification is a foundation for strategic career planning. Professionals can use the credential to advance in roles such as ERP consultant, functional analyst, finance or operations manager, and solution architect. Career development involves identifying goals, pursuing complementary certifications, and gaining experience across multiple Dynamics 365 modules.
Certified individuals can also pursue leadership positions by demonstrating proficiency in implementing integrated business solutions, managing projects, and guiding teams. Career planning should incorporate professional development, hands-on experience, and networking to maximize opportunities and achieve long-term goals. MB-300 certification serves as a stepping stone for continued growth and success within the Dynamics 365 ecosystem.
Successfully passing the Microsoft Dynamics 365: Core Finance and Operations MB-300 exam requires a comprehensive approach that combines theoretical understanding, practical experience, and strategic exam preparation. From understanding the exam objectives and mastering core finance and operations concepts to leveraging hands-on labs, practice exams, and online resources, each step plays a vital role in building the knowledge and confidence needed to succeed.
Preparation should focus not only on memorizing processes but also on applying knowledge in real-world scenarios, simulating workflows, and understanding how different modules integrate. Consistent practice, participation in study groups, and strategic review of key topics reinforce learning and ensure readiness for the exam. Mental and physical preparation, along with effective time management and exam-day strategies, help candidates perform at their best.
Beyond passing the exam, MB-300 certification validates expertise in Dynamics 365, enhances career prospects, and opens doors to advanced roles such as ERP consultant, functional analyst, or solution architect. Certified professionals can apply their knowledge to optimize business processes, implement integrated solutions, and contribute to organizational efficiency and success. Continuous learning and staying updated with platform changes ensure that the certification remains relevant and valuable throughout a professional’s career.
In essence, passing the MB-300 exam is not just a milestone but a foundation for ongoing growth and professional excellence in Microsoft Dynamics 365 Core Finance and Operations. With structured preparation, hands-on experience, and a commitment to continuous learning, aspiring candidates can confidently achieve certification and leverage it for long-term career advancement.
ExamSnap's Microsoft MB-300 Practice Test Questions and Exam Dumps, study guide, and video training course are complicated in premium bundle. The Exam Updated are monitored by Industry Leading IT Trainers with over 15 years of experience, Microsoft MB-300 Exam Dumps and Practice Test Questions cover all the Exam Objectives to make sure you pass your exam easily.

Microsoft Training Courses













































SPECIAL OFFER: GET 10% OFF
This is ONE TIME OFFER

A confirmation link will be sent to this email address to verify your login. *We value your privacy. We will not rent or sell your email address.
Download Free Demo of VCE Exam Simulator
Experience Avanset VCE Exam Simulator for yourself.
Simply submit your e-mail address below to get started with our interactive software demo of your free trial.