
SC-100: Microsoft Cybersecurity Architect
PDFs and exam guides are not so efficient, right? Prepare for your Microsoft examination with our training course. The SC-100 course contains a complete batch of videos that will provide you with profound and thorough knowledge related to Microsoft certification exam. Pass the Microsoft SC-100 test with flying colors.

Curriculum for SC-100 Certification Video Course
| Name of Video | Time |
|---|---|
 1. SC - 100 Microsoft Cybersecurity Architect - Course trailer |
0:42 |
| Name of Video | Time |
|---|---|
 1. Chapter 1: The role of a security Architect |
1:29 |
 2. Zero Trust Overview |
1:39 |
 3. Guiding principles of zero trust |
2:53 |
 4. Pillars of Zero Trust |
6:39 |
 5. MCRA - Identity |
3:50 |
 6. MCRA - SOC Tools |
3:05 |
 7. MCRA - Endpoint Security |
5:08 |
 8. MCRA - Hybrid Computing |
7:21 |
 9. MCRA - Information Protection |
4:06 |
 10. MCRA - People Security |
6:54 |
 11. MCRA - IoT and IT Security - II |
7:39 |
 12. CAF - Introduction |
2:20 |
 13. CAF - strategy |
5:57 |
 14. CAF - Planning |
4:58 |
 15. CAF - Readyness - Azure setup guide |
11:01 |
 16. CAF - Readyness - Azure Landing Zone |
9:17 |
 17. CAF Landing Zone Deployment - Lab Step By Step-I |
5:29 |
 18. CAF Landing Zone Deployment - Lab Step By Step-II |
26:54 |
 19. CAF - Adopt Phase |
2:17 |
 20. CAF - Governance |
13:16 |
 21. IT Transformations - Gap analysis |
3:43 |
 22. Security transformations |
7:51 |
 23. Design Security for resiliency strategy |
4:05 |
 24. The reliability Pillar |
4:06 |
 25. SC 100 Case study overview |
2:25 |
 26. SC 100 Case Study |
12:04 |
 27. Chapter 2: Design a security options strategy - overview |
1:26 |
 28. Security operations strategy overview |
3:03 |
 29. Security operations frameworks, processes and procedures |
3:32 |
 30. SecOps and the Leadership |
3:58 |
 31. People and Processes |
4:42 |
 32. Metrics and Its importance in SOC |
3:31 |
 33. Recommendations for Designing a logging and auditing security strategy |
6:24 |
 34. Cyber Kill Chain - An overview |
3:49 |
 35. Focus areas for SOC in hybrid computing |
1:51 |
 36. Unified operations in Hybrid clouds |
5:06 |
 37. Tiers in SecOps |
3:47 |
 38. Azure Tools for SecOps |
6:10 |
 39. SecOps - Best practices for SIEM _ SOAR |
9:22 |
 40. SecOPs- Best Practices for Network and Azure AD Monitoring |
4:04 |
 41. Incident Response - Best Practices |
2:27 |
 42. Recovery - Best Practices |
3:03 |
 43. Workflow Automation |
3:03 |
 44. Workflow Automation - Lab |
4:28 |
 45. Workflow Automation - Logic apps integration - Lab |
7:22 |
 46. Incident Management process- Overview |
5:51 |
 47. Incident Management process - Preparation |
2:46 |
 48. Incident Management Process - Detection and Analysis |
1:37 |
 49. Incident Management Process - Containment Eradication and recovery |
3:31 |
 50. Incident Management Process - Post - Incident Activity |
2:27 |
 51. Threat Intelligence and SOC |
3:48 |
 52. Threat intelligence in Sentinel |
1:52 |
 53. Threat intelligence in Defender for Endpoint |
5:08 |
 54. Threat Intelligence for IOT |
2:13 |
 55. Threat Intelligence in Defender for Cloud |
2:07 |
 56. Chapter2 Case Study |
8:47 |
 57. Chapter 3: Identity Security Strategy -Introduction |
01:10 |
 58. Identity Security Strategy Overview |
2:28 |
 59. Evolution of Identity Technology |
2:51 |
 60. Identity Challenges |
1:56 |
 61. Microsoft Identity Store - Overview |
5:30 |
 62. Identity Governance - Overview |
4:20 |
 63. Identity is the new control plane |
2:45 |
 64. Zero Trust Concepts and Principles |
2:43 |
 65. Zero Trust Components |
4:26 |
 66. Planning a Zero Trust Strategy |
3:29 |
 67. Zero Trust Model - Introduction |
1:07 |
 68. Enabling Zero Trust Model-II |
10:36 |
 69. Enabling Zero Trust Model-III |
4:01 |
 70. Zero trust Security strategy for Identities |
7:08 |
 71. Conditional Access support for Zero Trust Architecture |
3:22 |
 72. Conditional Access Personas |
6:01 |
 73. Secure Authentication Methods |
1:35 |
 74. Secure Authentication Methods - II |
1:35 |
 75. Password hash Sync - PHS |
8:38 |
 76. Pass Through Authentication - PTA |
9:51 |
 77. Azure AD Roles - Best Practices |
6:17 |
 78. Design a Security Strategy for Privileged Role Access |
2:20 |
 79. Develop a Roadmap |
2:09 |
 80. Develop a Roadmap - Explained |
5:33 |
 81. Design a security strategy for privileged activities |
4:34 |
 82. Rapid Modernization Plan - RAMP |
4:21 |
 83. Execute Critical strategic initiatives for Privileged Activity Management |
2:10 |
 84. Chapter Case Study 01 |
8:04 |
 85. Chapter Case Study 02 |
5:08 |
| Name of Video | Time |
|---|---|
 1. Evaluate Regulatory Compliance - Introduction |
1:17 |
 2. Interpret Compliance Requirements |
2:53 |
 3. Compliance Offerings |
6:10 |
 4. Evaluate infra compliance using defender for cloud |
3:44 |
 5. Design for data residency requirements |
5:01 |
 6. Encryption Support for various services |
6:25 |
 7. Chapter 1: Case Study |
7:29 |
 8. Chapter 2: Evaluate Security postures - Chapter Introduction |
1:00 |
 9. what is security posture |
3:04 |
 10. Azure Security Benchmark |
2:21 |
 11. Miter attack and Microsoft Defender for cloud |
3:44 |
 12. Security Hygiene for Cloud workloads |
5:57 |
 13. Security and policy options in Azure Landing zone |
2:37 |
 14. Chapter 2: Case Study |
11:32 |
| Name of Video | Time |
|---|---|
 1. Chapter 1 : Introduction |
1:13 |
 2. Plan and Implement a security strategy across teams |
7:19 |
 3. Security Role and Responsibilities |
4:59 |
 4. Building the cloud security strategy document - considerations |
5:41 |
 5. Security strategy document - deliverables |
2:41 |
 6. Security Strategy document - Best Practices |
4:28 |
 7. Continuous evolution of security strategy - Deliverables |
3:12 |
 8. Best Practices for Security Planning |
3:54 |
 9. Establishing Essential security practices |
2:28 |
 10. Security Management strategy |
1:53 |
 11. Continuous Assessment |
3:08 |
 12. Chapter 1 case study |
4:07 |
 13. Chapter 2 : Introduction |
0:54 |
 14. What is a Security Baseline |
2:02 |
 15. Security Baseline Principles |
4:31 |
 16. Security Requirement for servers |
3:11 |
 17. Securing Member Servers |
5:43 |
 18. Azure Security Benchmarks |
6:17 |
 19. Securing Mobile devices |
2:40 |
 20. Application Control |
2:11 |
 21. Device Settings using Intune |
3:07 |
 22. Other requirements for clients and endpoints |
1:46 |
 23. Securing Domain Controllers |
5:55 |
 24. Securing DCs from Attacks |
4:14 |
 25. Key Vault - Fundamentals |
3:19 |
 26. Managing access to secrets |
3:56 |
 27. Securing remote access |
3:50 |
 28. Security Ops - Best Practices |
2:58 |
 29. Importance of Interactions with Business leaders |
3:39 |
 30. Hiring right people with right mindset |
2:18 |
 31. Metrics linked to SOC team |
3:13 |
 32. Forensic Procedures and Endpoint Forensics |
4:32 |
 33. Chapter 2 Case Study |
4:34 |
 34. Chapter 3 Introduction |
0:48 |
 35. Security baselines for PaaS services |
6:48 |
 36. Security baselines for IaaS services |
5:27 |
 37. Security Baselines for SaaS Services |
4:42 |
 38. Security requirements for IOT based workloads |
6:31 |
 39. IOT Devices - Security Posture and Threat Management |
4:08 |
 40. Specify security requirements for data work loads |
4:52 |
 41. Security posture management for data related workloads |
5:59 |
 42. Security requirements for Web Based Workloads |
7:29 |
 43. Security posture management for App services |
2:33 |
 44. Security requirements for Azure Storage Accounts |
9:01 |
 45. Azure Defender for Storage |
2:21 |
 46. Security recommendations for Containers |
8:26 |
 47. Defender for Containers |
2:49 |
 48. Chapter 3 Case Study |
3:32 |
| Name of Video | Time |
|---|---|
 1. Threat Modelling - Introduction |
8:24 |
 2. Threat Modelling - Use Case |
10:49 |
 3. Understanding the application threat modelling |
2:38 |
 4. STRIDE Methodology |
3:58 |
 5. Mitigating the Identified threats |
2:04 |
 6. Shift from Waterfall to DevOps |
1:54 |
 7. DevOps & Its Phases |
4:20 |
 8. DevSecOps and its importance |
3:00 |
 9. Onboarding applications to Azure AD |
6:31 |
 10. Chapter 1 Case study |
5:11 |
 11. Chapter 2 Introduction |
1:26 |
 12. Mitigating threats to data |
4:25 |
 13. Ransomware protection |
1:52 |
 14. Ransomware protection - Phases |
6:26 |
 15. Strategy to identify and protect sensitive Data |
4:58 |
 16. Know your data with Microsoft Purview -I |
5:42 |
 17. Govern your data with Defender for cloud apps - II |
6:33 |
 18. Govern your data - Data Retention |
5:05 |
 19. Govern your data - Records Management |
7:33 |
 20. Chapter 2 case study |
5:43 |
Microsoft SC-100 Exam Dumps, Practice Test Questions
100% Latest & Updated Microsoft SC-100 Practice Test Questions, Exam Dumps & Verified Answers!
30 Days Free Updates, Instant Download!
SC-100 Premium Bundle
- Premium File: 349 Questions & Answers. Last update: May 12, 2026
- Training Course: 168 Video Lectures
- Study Guide: 436 Pages
- Latest Questions
- 100% Accurate Answers
- Fast Exam Updates
Microsoft SC-100 Training Course
Want verified and proven knowledge for Microsoft Cybersecurity Architect? Believe it's easy when you have ExamSnap's Microsoft Cybersecurity Architect certification video training course by your side which along with our Microsoft SC-100 Exam Dumps & Practice Test questions provide a complete solution to pass your exam Read More.
Comprehensive Microsoft SC-100 Course: Identity Management and Threat Protection
Microsoft SC-100 Cybersecurity Architect Certification Training
Course Overview
The Microsoft SC-100 certification is designed for professionals who aim to become experts in Microsoft security technologies, identity, and compliance management. This training course provides an in-depth understanding of the principles and practices required to manage security, governance, and compliance solutions effectively across Microsoft environments. It is tailored for IT professionals, security engineers, and administrators who are responsible for designing and implementing security strategies, managing identity and access, and ensuring data protection in cloud and hybrid environments.
This course serves as a complete roadmap for preparing for the Microsoft SC-100 exam. It focuses on practical implementation as well as conceptual knowledge, helping learners gain hands-on experience while mastering the theoretical foundations of Microsoft security architectures. Students will explore various tools, technologies, and strategies that are integral to maintaining a secure digital environment.
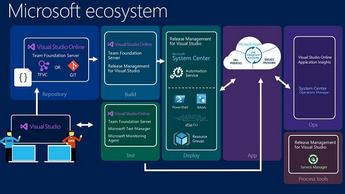
The SC-100 course emphasizes real-world scenarios, enabling learners to apply their knowledge to complex enterprise environments. It introduces a variety of Microsoft solutions, including Azure Active Directory, Microsoft Information Protection, threat protection tools, and compliance frameworks, ensuring that participants understand how to integrate these technologies into a cohesive security strategy.
With this course, learners will gain a comprehensive understanding of the security landscape within Microsoft ecosystems, equipping them with the skills to manage access control, monitor threats, protect sensitive information, and implement governance policies. By combining theoretical knowledge with practical exercises, the course ensures participants are well-prepared for the challenges of securing modern enterprise environments.
What You Will Learn From This Course
Gain a deep understanding of Microsoft security technologies and their applications in enterprise environments.
Learn to design, implement, and manage identity and access management solutions using Azure Active Directory and related tools.
Understand the principles of Zero Trust security and how to apply them across cloud and hybrid infrastructures.
Develop skills in data classification, information protection, and compliance strategies to safeguard sensitive information.
Explore advanced threat protection techniques and tools to monitor, detect, and respond to security incidents.
Learn to design governance and compliance frameworks that meet regulatory and organizational requirements.
Prepare effectively for the Microsoft SC-100 certification exam through hands-on labs, real-world scenarios, and practical exercises.
Understand how to integrate Microsoft security technologies to create a comprehensive security and compliance strategy.
Gain the knowledge needed to advise stakeholders and guide organizations in implementing best practices for secure digital transformation.
Learning Objectives
Upon completing this course, participants will be able to:
Evaluate organizational security needs and design appropriate security strategies using Microsoft technologies.
Implement identity and access management solutions, including multi-factor authentication, conditional access, and hybrid identity integration.
Apply the principles of Zero Trust architecture to protect cloud and on-premises resources.
Design and implement information protection strategies, including data classification, labeling, and encryption, aligned with compliance requirements.
Monitor and respond to security threats using Microsoft security tools, including advanced threat analytics and reporting.
Develop governance strategies that ensure compliance with industry standards, regulations, and organizational policies.
Prepare for and succeed in the SC-100 certification exam by applying theoretical knowledge in practical scenarios.
Advise organizational stakeholders on security policies, identity management, and data protection practices.
Integrate Microsoft security technologies into a unified security framework for enterprise environments.
Continuously assess and improve security posture using Microsoft security solutions and best practices.
Requirements
This course is designed for IT professionals with foundational knowledge of Microsoft technologies. Participants should have experience with cloud computing, network administration, and security concepts. While no specific prior certification is mandatory, familiarity with Microsoft Azure services, Microsoft 365 environments, and basic cybersecurity principles is highly recommended.
To successfully complete this course, learners should have:
Basic understanding of networking concepts, including firewalls, VPNs, and network protocols.
Familiarity with cloud computing platforms, particularly Microsoft Azure and Microsoft 365.
Understanding of common security principles, such as authentication, authorization, encryption, and identity management.
Experience working with Windows Server environments, Active Directory, and related Microsoft tools.
Basic knowledge of compliance regulations and standards relevant to IT security, such as GDPR, ISO 27001, and NIST frameworks.
Course Description
The Microsoft SC-100 Training Course is a comprehensive learning program that equips IT professionals with the knowledge and skills needed to design and implement security, compliance, and identity solutions across Microsoft platforms. This course covers all domains of the SC-100 certification exam, including designing a Zero Trust strategy, evaluating security posture, and implementing governance and compliance frameworks.
The curriculum is structured to balance theoretical understanding with practical application. Participants will engage in hands-on exercises, labs, and scenario-based challenges that simulate real-world enterprise security environments. Through this approach, learners not only prepare for the certification exam but also acquire the practical skills necessary to secure cloud and hybrid infrastructures effectively.
The course content spans multiple core areas of Microsoft security. It begins with foundational concepts of identity and access management, exploring Azure Active Directory, hybrid identity integration, multi-factor authentication, and conditional access policies. Learners then progress to advanced topics, including threat protection, security monitoring, information protection, compliance frameworks, and governance strategies.
Additionally, the course introduces learners to Microsoft security tools and technologies such as Microsoft Defender, Microsoft Purview, Microsoft Sentinel, and other integrated solutions that facilitate proactive threat management and compliance monitoring. Participants will gain insights into how these tools interact and complement each other, enabling them to design a cohesive security strategy that addresses organizational needs.
Practical exercises form a critical part of the course, allowing learners to apply concepts in controlled lab environments. These exercises include implementing identity solutions, configuring access controls, deploying information protection policies, and responding to simulated security incidents. This hands-on approach ensures that participants are confident in their ability to manage real-world security challenges.
Throughout the course, learners will also explore governance and compliance best practices. Topics include designing policies to meet regulatory requirements, conducting security assessments, auditing user activity, and developing continuous improvement strategies. By integrating governance with technical security measures, learners will understand how to maintain a secure and compliant enterprise environment over time.
The Microsoft SC-100 course is ideal for professionals seeking career advancement in security architecture, cloud security, and IT compliance. It provides the knowledge and experience necessary to advise organizations on implementing Microsoft security technologies effectively, ensuring data protection, regulatory compliance, and robust identity management.
Target Audience
The Microsoft SC-100 Training Course is tailored for a wide range of IT professionals who are responsible for implementing, managing, and advising on security and compliance strategies within Microsoft environments. The primary target audience includes:
Security architects seeking to enhance their expertise in Microsoft security technologies and strategies.
IT administrators and engineers responsible for managing Azure Active Directory, identity solutions, and access management policies.
Compliance officers and IT auditors who require a deep understanding of governance frameworks, information protection, and regulatory requirements.
Cloud administrators and security professionals tasked with securing hybrid and cloud environments.
Professionals preparing for the SC-100 certification exam and seeking a structured, comprehensive training program.
Organizations aiming to develop internal expertise in Microsoft security technologies for operational and strategic purposes.
IT managers and consultants who advise clients on security best practices and regulatory compliance.
By targeting this audience, the course ensures that participants gain practical and actionable knowledge that can be directly applied to their current roles or used to advance their careers in Microsoft security and compliance.
Prerequisites
While the Microsoft SC-100 course is designed to be accessible, certain prerequisites will help participants maximize their learning experience and successfully complete the program. These prerequisites include:
Basic knowledge of networking concepts, including firewalls, routing, VPNs, and network protocols.
Familiarity with Microsoft cloud services such as Azure and Microsoft 365.
Understanding of fundamental cybersecurity principles, including authentication, authorization, encryption, and threat mitigation.
Experience with Windows Server environments, Active Directory, and directory services.
Awareness of common compliance standards and regulations, such as GDPR, HIPAA, ISO 27001, and NIST frameworks.
Experience in administering user accounts, managing permissions, and implementing basic security policies in enterprise environments.
Willingness to engage in hands-on exercises and practical labs to reinforce theoretical concepts.
Participants who meet these prerequisites will be better prepared to navigate advanced topics, complete lab exercises efficiently, and apply their knowledge to real-world scenarios.
The course does not assume prior experience with Microsoft SC-100, making it suitable for motivated learners who meet the basic technical prerequisites and are eager to specialize in Microsoft security technologies and identity management.
Key Topics Covered in the Course
The Microsoft SC-100 Training Course covers several essential topics that align with the SC-100 exam objectives and real-world security practices. These topics include:
Identity and Access Management: Azure Active Directory, hybrid identity integration, multi-factor authentication, conditional access policies, identity protection, and role-based access control.
Security Architecture Design: Principles of Zero Trust security, secure network design, threat protection strategies, and integration of security technologies.
Information Protection: Data classification, labeling, encryption, and Microsoft Information Protection tools to safeguard sensitive information.
Threat Detection and Response: Monitoring, analyzing, and responding to security incidents using Microsoft Defender, Microsoft Sentinel, and advanced analytics.
Governance and Compliance: Designing governance frameworks, auditing and reporting, regulatory compliance, and continuous improvement strategies.
Practical Labs and Hands-On Exercises: Realistic scenarios for identity management, access control, threat detection, information protection, and compliance implementation.
The course integrates these topics into a cohesive learning experience, ensuring that participants understand the interrelationships between identity, access, security, and compliance in Microsoft ecosystems.
Course Modules/Sections
The Microsoft SC-100 training course is designed with a modular structure that allows learners to progressively develop expertise in identity and access management. Each module builds upon the previous one, ensuring a thorough understanding of both foundational and advanced concepts. The course begins with an introduction to identity management and the principles of authentication and authorization, providing a strong base for more complex topics.
The first module focuses on Azure Active Directory, exploring how to manage users, groups, and roles effectively. Participants learn to implement identity governance, configure directory synchronization with on-premises environments, and manage hybrid identity solutions. The module also introduces the concept of conditional access, helping learners understand how to enforce policies that enhance security while maintaining user productivity.
The second module delves into multi-factor authentication and advanced access management strategies. Participants explore methods to strengthen authentication processes, integrate third-party identity providers, and implement adaptive access controls based on user behavior and risk assessment. Real-world scenarios are incorporated to demonstrate how these strategies protect enterprise environments from unauthorized access and security breaches.
In the third module, learners focus on identity protection and threat mitigation. They study tools and techniques for monitoring identity activity, detecting suspicious behavior, and responding to security incidents. This module also emphasizes the importance of continuous improvement and proactive security management, enabling participants to maintain a resilient identity infrastructure.
The final module integrates all aspects of identity and access management into a cohesive security strategy. Participants learn to design enterprise-wide identity solutions, implement access controls, and ensure compliance with organizational policies and regulatory requirements. The module concludes with hands-on labs and scenario-based exercises, allowing learners to apply theoretical knowledge in practical settings and prepare for the SC-100 certification exam.
Key Topics Covered
This course covers a comprehensive range of topics related to identity and access management, ensuring that participants develop both practical and theoretical expertise. Key topics include the fundamentals of Azure Active Directory, hybrid identity integration, user and group management, role-based access control, and directory synchronization. Learners explore authentication methods, multi-factor authentication, conditional access policies, and single sign-on solutions.
The course also covers identity protection, including threat detection, risk assessment, and monitoring of user behavior. Participants gain hands-on experience configuring identity protection policies, investigating alerts, and responding to security incidents. Best practices for securing identities, managing privileged accounts, and mitigating risks associated with compromised credentials are also emphasized.
Additional topics include governance and compliance considerations, such as ensuring that identity management practices align with organizational policies and regulatory requirements. Learners explore how to implement access reviews, audit user activity, and design policies that balance security and usability. The course also covers emerging trends in identity and access management, helping participants stay current with new technologies and evolving threat landscapes.
By the end of the course, learners have a complete understanding of how to design, implement, and manage identity and access management solutions within Microsoft environments. They are prepared to address real-world security challenges, protect enterprise resources, and contribute to organizational governance and compliance initiatives.
Teaching Methodology
The teaching methodology for the Microsoft SC-100 course combines theoretical instruction with practical application to ensure comprehensive learning. Concepts are introduced through detailed explanations, real-world examples, and case studies that illustrate how identity and access management strategies are applied in enterprise environments. Lectures are structured to gradually build knowledge, starting with foundational topics and progressing to advanced strategies, allowing learners to develop a strong conceptual understanding before engaging in hands-on exercises.
Practical labs are a core component of the methodology, providing participants with the opportunity to implement identity and access management solutions in controlled environments. These labs simulate real-world scenarios, enabling learners to practice configuring Azure Active Directory, implementing conditional access policies, integrating on-premises and cloud identities, and responding to security alerts. By engaging in hands-on exercises, participants gain confidence in applying their knowledge to real enterprise settings.
Interactive discussions and scenario-based exercises encourage learners to think critically about security challenges and devise effective solutions. Case studies highlight common issues encountered in identity and access management, such as compromised accounts, insider threats, and policy enforcement challenges. Participants are encouraged to analyze these scenarios, propose solutions, and discuss outcomes, fostering collaboration and problem-solving skills.
Supplementary resources, including guides, documentation, and practice exercises, support self-paced learning. Learners can review concepts, explore advanced configurations, and test their understanding through quizzes and exercises. The combination of lectures, practical labs, discussions, and self-study ensures that participants develop both the theoretical knowledge and practical skills necessary to succeed in identity and access management roles and to pass the SC-100 certification exam.
Assessment & Evaluation
Assessment and evaluation in the Microsoft SC-100 course are designed to measure both theoretical understanding and practical competence in identity and access management. Participants are evaluated through a combination of quizzes, hands-on lab exercises, scenario-based challenges, and practice exams. Each assessment is aligned with the core learning objectives of the course, ensuring that participants demonstrate mastery of critical skills required for real-world enterprise environments.
Quizzes are used to assess comprehension of foundational concepts, such as authentication, authorization, and Azure Active Directory features. These quizzes help learners reinforce knowledge, identify areas that require further study, and track their progress throughout the course. Questions are designed to reflect the types of scenarios and problem-solving tasks encountered in the SC-100 certification exam, providing practical exam preparation.
Hands-on lab exercises form a key part of evaluation, allowing learners to demonstrate their ability to implement identity and access management solutions in practical settings. Labs include configuring user accounts, managing groups and roles, implementing conditional access policies, and integrating hybrid identity environments. Performance in these exercises is assessed based on accuracy, efficiency, and adherence to best practices, ensuring that participants can apply theoretical knowledge effectively.
Scenario-based challenges present complex, real-world security problems that require learners to analyze situations, identify potential risks, and propose appropriate solutions. These assessments encourage critical thinking, problem-solving, and decision-making skills, which are essential for security architects and IT professionals responsible for managing enterprise identities. Participants receive feedback on their approach, highlighting strengths and areas for improvement, which fosters continuous learning and skill development.
Practice exams simulate the SC-100 certification experience, providing participants with an opportunity to apply their knowledge under timed conditions. These exams help learners become familiar with question formats, manage time effectively, and identify topics that require additional focus. By combining quizzes, labs, scenario-based exercises, and practice exams, the course ensures that participants are well-prepared to succeed in both practical applications and certification assessments.
Identity Fundamentals
Understanding the fundamentals of identity is critical for implementing secure access management strategies. The course begins with an overview of identity concepts, including authentication, authorization, and directory services. Participants learn how identities are represented within Microsoft ecosystems, how authentication protocols function, and how authorization determines access to resources.
Azure Active Directory is introduced as the central identity management platform for Microsoft environments. Participants explore its architecture, key components, and capabilities, including user and group management, application integration, and directory synchronization. Hybrid identity scenarios are also covered, demonstrating how on-premises and cloud identities can be integrated seamlessly.
Participants learn the importance of identity governance, including policies for user provisioning, access reviews, and role-based access control. These practices ensure that users have appropriate access to resources while minimizing the risk of unauthorized access. Real-world examples illustrate how identity governance policies can prevent security breaches and maintain compliance with regulatory requirements.
Authentication and Access Control
Authentication and access control are central to securing enterprise environments. Participants study different authentication methods, including password-based authentication, multi-factor authentication, and certificate-based authentication. The course emphasizes the importance of multi-factor authentication in mitigating the risk of credential compromise and enhancing security across cloud and hybrid environments.
Conditional access policies are explored in depth, showing how organizations can enforce access controls based on user location, device compliance, risk levels, and other contextual factors. Participants gain hands-on experience creating and testing conditional access policies, ensuring that they can implement robust security measures that balance protection with user convenience.
Single sign-on solutions are also covered, demonstrating how users can access multiple applications and services using a single set of credentials. Participants learn how to configure single sign-on for enterprise applications, reducing the complexity of user management while enhancing security.
Identity Protection and Threat Mitigation
Protecting identities from compromise is a key focus of the course. Participants learn to use Microsoft identity protection tools to monitor user activity, detect suspicious behavior, and respond to potential threats. Risk assessment techniques are covered, helping learners understand how to prioritize threats and implement appropriate mitigation strategies.
The course includes hands-on exercises in configuring alerts, investigating security incidents, and remediating compromised accounts. Participants explore best practices for securing privileged accounts, managing role assignments, and enforcing strong authentication methods. Scenario-based exercises illustrate how attackers may attempt to exploit identities, and learners practice defending against these threats using Microsoft security technologies.
Continuous monitoring and proactive management are emphasized to ensure that identities remain secure over time. Participants learn how to leverage reporting tools, audit logs, and analytics to maintain visibility into identity activity and detect anomalies that may indicate security risks.
Hybrid Identity Integration
Many organizations operate in hybrid environments where on-premises and cloud identities must coexist. Participants explore strategies for integrating on-premises directories with Azure Active Directory, including directory synchronization, federation, and single sign-on configurations.
The course covers common challenges in hybrid identity environments, such as conflicting attributes, latency issues, and synchronization errors. Participants gain practical experience resolving these challenges through lab exercises and guided simulations. Best practices for maintaining hybrid identity solutions are discussed, including monitoring synchronization processes, managing directory objects, and enforcing consistent security policies across environments.
Governance and Compliance in Identity Management
Effective governance ensures that identity management practices align with organizational policies and regulatory requirements. Participants learn to design access reviews, implement policy enforcement, and conduct audits of identity-related activities. The course emphasizes the importance of balancing security with usability, ensuring that access controls do not impede productivity while maintaining compliance.
Learners explore tools for auditing and reporting, including activity logs, security dashboards, and compliance reports. Scenario-based exercises demonstrate how governance practices can prevent unauthorized access, detect policy violations, and support regulatory compliance efforts. Participants also learn strategies for continuous improvement, including periodic reviews, policy updates, and training programs to maintain a secure and compliant identity environment.
Benefits of the Course
The Microsoft SC-100 course provides numerous benefits for IT professionals, security engineers, and administrators looking to enhance their skills in Microsoft security technologies. One of the primary advantages is gaining a comprehensive understanding of identity and access management, information protection, threat monitoring, and compliance strategies across cloud and hybrid environments. Participants learn to implement best practices that ensure organizational security while optimizing operational efficiency.
Another benefit is the opportunity to prepare thoroughly for the SC-100 certification exam. The course aligns with exam objectives, covering all key domains including designing a Zero Trust strategy, evaluating security posture, and implementing governance frameworks. By the end of the training, participants will have the knowledge and practical experience necessary to confidently approach the certification exam and increase their chances of passing on the first attempt.
The course also enhances career prospects and opens up opportunities for roles such as security architect, cloud security engineer, identity and access management specialist, and compliance officer. Organizations increasingly value professionals with expertise in Microsoft security technologies due to the growing complexity of cloud environments and the rising prevalence of cyber threats. By completing this course, participants demonstrate their ability to design, implement, and manage robust security solutions that protect organizational assets.
Participants gain hands-on experience with Microsoft tools and technologies through practical labs and scenario-based exercises. This practical exposure ensures that learners can apply theoretical knowledge to real-world situations, bridging the gap between classroom learning and professional application. They become proficient in using Microsoft Defender, Microsoft Sentinel, Microsoft Information Protection, and Azure Active Directory to monitor, detect, and respond to security threats.
Additionally, the course fosters a mindset of proactive security management. Learners develop the skills to anticipate potential vulnerabilities, implement preventive measures, and maintain continuous monitoring of security systems. This approach helps organizations reduce the risk of breaches, protect sensitive information, and comply with regulatory requirements. By equipping participants with these capabilities, the course not only prepares them for certification but also for meaningful contributions to organizational security initiatives.
Networking and collaboration opportunities are also an important benefit. Participants engage in interactive discussions, group exercises, and peer collaboration, which allows them to learn from others’ experiences and gain diverse perspectives on security challenges. This collaborative environment fosters problem-solving skills, encourages knowledge sharing, and strengthens the professional community around Microsoft security practices.
Course Duration
The Microsoft SC-100 course is structured to provide comprehensive coverage of all essential topics while allowing sufficient time for practical exercises and knowledge consolidation. Typically, the course spans several weeks, with a recommended pace of study that balances depth of understanding with the ability to apply concepts in hands-on environments. Learners can expect the course duration to range from 40 to 60 hours of instructional time, depending on the learning format and individual study pace.
The course is divided into modules that allow participants to focus on specific areas of identity and access management, information protection, threat monitoring, and governance. Each module is designed to build upon the previous one, ensuring a logical progression from foundational concepts to advanced strategies. This modular structure allows learners to manage their time effectively and ensures that they thoroughly understand each topic before moving on to the next.
Practical lab sessions are an integral part of the course and are included in the total duration. These labs typically require additional time beyond the instructional sessions, as learners work through scenarios, configure tools, and implement policies. Allocating sufficient time for these exercises ensures that participants gain hands-on experience and develop the confidence to apply their knowledge in real-world settings.
Self-paced learning options are often available, allowing participants to extend the course duration according to their schedules and learning preferences. This flexibility is particularly beneficial for working professionals who need to balance training with job responsibilities. Participants can revisit modules, repeat lab exercises, and review supplementary materials as needed to reinforce learning and ensure mastery of the content.
Regular assessment and evaluation are embedded throughout the course duration to track progress and identify areas that may require additional focus. Participants receive feedback on quizzes, lab exercises, and scenario-based challenges, enabling them to adjust their study approach and achieve optimal outcomes. By the end of the course duration, learners are well-prepared for the SC-100 certification exam and equipped with practical skills to implement security, identity, and compliance solutions effectively.
Tools & Resources Required
To maximize the benefits of the Microsoft SC-100 course, participants need access to specific tools and resources that enable hands-on practice and effective learning. A fundamental requirement is a Microsoft Azure subscription, which provides access to Azure Active Directory, Microsoft Defender, Microsoft Sentinel, and other essential services. This subscription allows learners to create and configure environments, implement policies, and conduct lab exercises.
Participants also need access to Microsoft 365 environments, which are integral for understanding information protection, compliance, and governance strategies. Microsoft 365 provides tools for data classification, labeling, monitoring, and reporting, allowing learners to gain practical experience in securing enterprise data. Access to administrative privileges within these environments is recommended to perform hands-on tasks effectively.
A stable internet connection and a computer capable of running web-based portals, virtual machines, and lab environments are essential. Learners should ensure that their systems meet the minimum requirements for accessing Azure and Microsoft 365 services without interruptions. Utilizing cloud-based lab environments provided as part of the course can also facilitate hands-on exercises without requiring extensive local resources.
Documentation and learning guides are important resources for participants. Microsoft provides extensive documentation, tutorials, and best practice guides for Azure, Microsoft 365, and security tools. These resources complement course materials and offer in-depth explanations, examples, and configuration guidance that reinforce learning. Participants are encouraged to explore these documents as part of self-paced study and exam preparation.
Additional tools such as PowerShell, Azure CLI, and security monitoring dashboards are used throughout the course to implement advanced configurations, automate tasks, and analyze security data. Familiarity with these tools enhances learners’ ability to perform hands-on exercises and manage complex environments efficiently. Lab instructions and scenario guides provided as part of the course serve as structured resources to guide learners through practical exercises, ensuring that they understand the objectives and outcomes of each activity.
Collaboration platforms, discussion forums, and peer learning resources are also valuable for participants. These platforms allow learners to ask questions, share insights, and engage with instructors and peers, enhancing the overall learning experience. Access to practice exams and simulation tools further supports preparation for the SC-100 certification, allowing participants to test their knowledge under exam-like conditions.
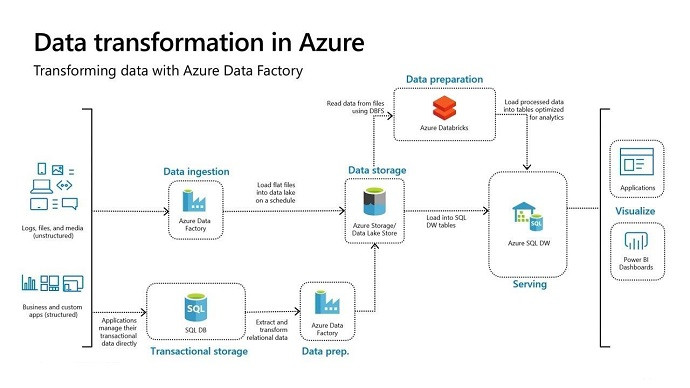
Information Protection and Classification
A critical component of Microsoft SC-100 training is understanding how to protect organizational information and ensure compliance with regulatory requirements. Participants learn to implement Microsoft Information Protection tools to classify, label, and secure sensitive data. These tools enable organizations to enforce policies that control access to information, prevent unauthorized sharing, and maintain compliance with industry regulations.
The course covers strategies for data classification, including identifying sensitive information, applying appropriate labels, and configuring policies that enforce security controls. Participants gain hands-on experience in configuring Microsoft 365 information protection settings, defining retention policies, and implementing encryption methods. Real-world examples illustrate how these practices protect critical organizational data and reduce the risk of breaches.
Participants also explore techniques for monitoring and auditing data usage, including tracking file access, detecting policy violations, and generating compliance reports. These capabilities allow organizations to maintain visibility into information flows, ensure adherence to governance policies, and respond proactively to potential security incidents. Hands-on exercises reinforce these skills by simulating scenarios where learners must classify, protect, and monitor data according to defined policies.
The course emphasizes the integration of information protection with identity and access management. By linking classification and labeling policies with access controls, learners understand how to create a cohesive security strategy that safeguards sensitive data while enabling authorized users to access information efficiently. Scenario-based exercises highlight challenges such as data leakage prevention, insider threats, and secure collaboration, providing participants with practical strategies to address these issues.
Threat Detection and Response
Monitoring, detecting, and responding to threats is a core aspect of Microsoft SC-100 training. Participants learn to leverage Microsoft security tools, including Microsoft Defender and Microsoft Sentinel, to gain real-time visibility into potential threats and vulnerabilities. The course covers advanced threat analytics, automated alerting, and incident response strategies that allow organizations to mitigate risks effectively.
Hands-on labs provide practical experience in configuring security monitoring dashboards, setting up alerting rules, and investigating potential security incidents. Participants practice responding to simulated threats, analyzing logs, and implementing remediation measures. These exercises build confidence in using Microsoft security tools to maintain a secure environment and respond proactively to emerging threats.
The course also emphasizes the importance of continuous threat assessment and proactive security management. Participants learn to conduct regular security evaluations, identify vulnerabilities, and implement preventive measures. Best practices for integrating threat detection with identity and access management and information protection ensure a comprehensive approach to enterprise security.
Scenario-based exercises simulate complex threat scenarios, such as phishing attacks, credential compromise, and insider threats. Participants apply their knowledge to investigate incidents, identify root causes, and implement corrective actions. These exercises enhance problem-solving skills and demonstrate how to leverage Microsoft security technologies to maintain organizational resilience.
Governance and Compliance
Effective governance and compliance practices are essential for managing security in Microsoft environments. The course covers strategies for designing governance frameworks, enforcing policies, and ensuring compliance with industry regulations and organizational standards. Participants learn to implement access reviews, audit user activity, and maintain documentation that supports regulatory compliance.
Hands-on exercises and case studies illustrate how governance practices can prevent unauthorized access, detect policy violations, and maintain accountability. Participants explore methods for integrating governance with technical security controls, such as conditional access, identity protection, and information classification. This integration ensures that security and compliance objectives are aligned, reducing organizational risk and supporting regulatory adherence.
The course also addresses the ongoing nature of governance and compliance, emphasizing continuous improvement. Participants learn to review policies regularly, update configurations based on evolving threats, and conduct periodic assessments to maintain a secure and compliant environment. By combining governance, compliance, and technical security measures, learners develop a holistic understanding of enterprise security management.
Practical Labs and Scenario Exercises
Hands-on labs and scenario exercises form an essential part of the learning experience in the Microsoft SC-100 course. These practical activities allow participants to apply theoretical knowledge in controlled environments, reinforcing understanding and building confidence in real-world application. Labs include configuring Azure Active Directory, implementing conditional access, deploying information protection policies, monitoring threats, and responding to simulated incidents.
Scenario-based exercises challenge learners to solve complex security problems, such as mitigating insider threats, responding to phishing attacks, and securing sensitive data. Participants are guided through step-by-step processes to analyze situations, implement solutions, and evaluate outcomes. These exercises enhance problem-solving skills and provide insights into the practical challenges of managing enterprise security.
The combination of practical labs and scenario exercises ensures that learners are not only prepared for the SC-100 certification exam but also equipped with the skills to implement effective security, identity, and compliance strategies in professional environments.
Career Opportunities
Completing the Microsoft SC-100 course opens a wide range of career opportunities for IT professionals and security specialists. The certification validates expertise in Microsoft security technologies, identity and access management, information protection, and compliance strategies, making participants highly valuable to organizations managing cloud and hybrid environments. Career paths include security architect, cloud security engineer, identity and access management specialist, compliance officer, and IT security consultant.
Security architects are responsible for designing and implementing comprehensive security strategies that protect enterprise resources while aligning with organizational policies. Professionals in this role leverage knowledge gained from SC-100 training to develop Zero Trust architectures, implement identity protection measures, and manage access across cloud and on-premises environments. Cloud security engineers focus on safeguarding cloud infrastructure, using tools such as Azure Active Directory, Microsoft Defender, and Microsoft Sentinel to monitor, detect, and respond to threats.
Identity and access management specialists apply skills learned in the course to manage user authentication, conditional access policies, and privileged accounts. They ensure that only authorized users can access critical resources while reducing the risk of breaches. Compliance officers use their understanding of governance frameworks and regulatory standards to develop policies, audit systems, and maintain organizational adherence to industry requirements. IT security consultants provide guidance and expertise to organizations on implementing Microsoft security solutions, creating secure digital environments, and addressing complex security challenges.
In addition to specialized roles, SC-100 certification enhances prospects for career advancement and salary growth. Organizations increasingly prioritize professionals with verified expertise in Microsoft security solutions due to rising cyber threats and regulatory pressures. Certified individuals are often considered for leadership positions, project management roles, and strategic advisory functions that influence security and compliance decisions across the enterprise.
The certification also demonstrates commitment to professional development, making participants more competitive in the job market. Employers recognize SC-100 certified professionals as knowledgeable, skilled, and capable of applying best practices to safeguard organizational assets. By completing this course, learners position themselves as key contributors to the security and success of their organizations, while also gaining the flexibility to explore diverse roles within IT security, compliance, and cloud administration.
Enroll Today
Enrolling in the Microsoft SC-100 training course is the first step toward mastering Microsoft security technologies and advancing your career. The course provides a structured, comprehensive learning path, combining theoretical instruction with hands-on labs, scenario-based exercises, and real-world examples. Participants gain the skills necessary to implement identity and access management, information protection, threat monitoring, and governance strategies across enterprise environments.
The course is designed to accommodate working professionals and learners with varying levels of experience. Flexible learning options, including instructor-led sessions, self-paced modules, and interactive labs, allow participants to tailor their study schedules to fit their needs. Enrolling today provides immediate access to all course materials, practical exercises, and resources required to gain expertise in Microsoft security solutions and prepare for the SC-100 certification exam.
By enrolling, participants join a community of IT professionals committed to security excellence. Collaborative discussions, peer learning, and instructor guidance enhance the learning experience and provide valuable insights into practical security challenges. The course equips learners with the confidence and skills to design, implement, and manage secure Microsoft environments, positioning them for success in both professional roles and certification objectives.
Investing in this course represents a strategic step toward career growth, professional recognition, and mastery of Microsoft security technologies. Participants gain not only certification preparation but also the practical experience required to make a tangible impact in their organizations. Enroll today to take control of your professional development, enhance your expertise, and secure your future in the rapidly evolving field of IT security.
Prepared by Top Experts, the top IT Trainers ensure that when it comes to your IT exam prep and you can count on ExamSnap Microsoft Cybersecurity Architect certification video training course that goes in line with the corresponding Microsoft SC-100 exam dumps, study guide, and practice test questions & answers.
Purchase Individually




Microsoft Training Courses












































Only Registered Members can View Training Courses
Please fill out your email address below in order to view Training Courses. Registration is Free and Easy, You Simply need to provide an email address.
- Trusted by 1.2M IT Certification Candidates Every Month
- Hundreds Hours of Videos
- Instant download After Registration






